A simple detail about password cracking tools from the wiki. In cryptanalysis and computer security, password cracking is the process of recovering passwords from data that have been stored in or transmitted by a computer system. A standard approach (brute-force attack) is to try guesses repeatedly for the password and check them against an available cryptographic hash of the password. What is Password Cracking? Password cracking is the process of guessing or recovering a password from stored locations or from data transmission system. It is used to get a password for unauthorized access or to recover a forgotten password. In penetration testing, it is used to check the security of an application.
- Email Password Cracker
- Dictionary Based Password Cracker
- Password Cracker No Download
- 7z Password Dictionary Cracker
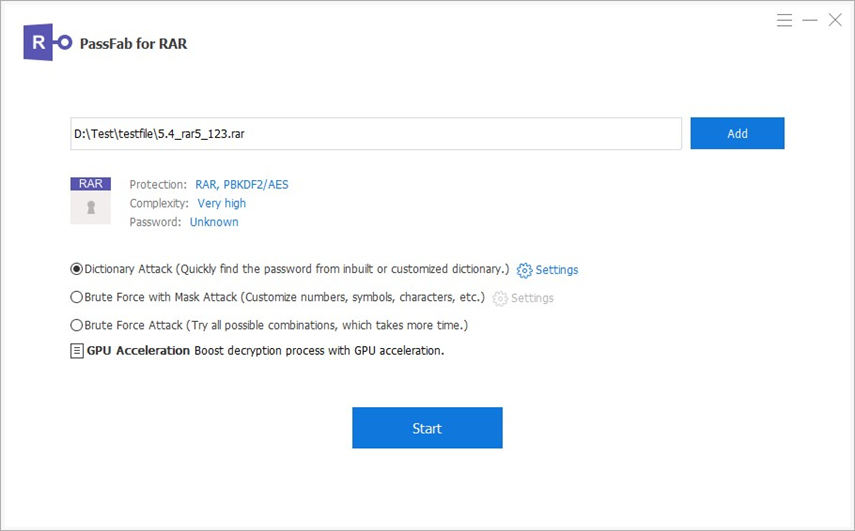
- Dictionary File Rar Password Cracker
In cryptanalysis and computer security, a dictionary attack is a form of brute force attack technique for defeating a cipher or authentication mechanism by trying to determine its decryption key or passphrase by trying hundreds or sometimes millions of likely possibilities, such as words in a dictionary.
Email Password Cracker
Technique[edit]
A dictionary attack is based on trying all the strings in a pre-arranged listing, typically derived from a list of words such as in a dictionary (hence the phrase dictionary attack).[1]In contrast to a brute force attack, where a large proportion of the key space is searched systematically, a dictionary attack tries only those possibilities which are deemed most likely to succeed. Dictionary attacks often succeed because many people have a tendency to choose short passwords that are ordinary words or common passwords, or simple variants obtained, for example, by appending a digit or punctuation character. Dictionary attacks are relatively easy to defeat, e.g. by using a passphrase or otherwise choosing a password that is not a simple variant of a word found in any dictionary or listing of commonly used passwords.
Pre-computed dictionary attack/Rainbow table attack[edit]
It is possible to achieve a time–space tradeoff by pre-computing a list of hashes of dictionary words, and storing these in a database using the hash as the key. This requires a considerable amount of preparation time, but allows the actual attack to be executed faster. The storage requirements for the pre-computed tables were once a major cost, but are less of an issue today because of the low cost of disk storage. Pre-computed dictionary attacks are particularly effective when a large number of passwords are to be cracked. The pre-computed dictionary need be generated only once, and when it is completed, password hashes can be looked up almost instantly at any time to find the corresponding password. A more refined approach involves the use of rainbow tables, which reduce storage requirements at the cost of slightly longer lookup-times. SeeLM hash for an example of an authentication system compromised by such an attack.

Dictionary Based Password Cracker
Pre-computed dictionary attacks, or 'rainbow table attacks', can be thwarted by the use of salt, a technique that forces the hash dictionary to be recomputed for each password sought, making precomputation infeasible, provided the number of possible salt values is large enough.

Dictionary attack software[edit]
See also[edit]
Password Cracker No Download
References[edit]
7z Password Dictionary Cracker
External links[edit]
- RFC 2828 – Internet Security Glossary
- RFC 4949 – Internet Security Glossary, Version 2